
When Notre Dame senior Christina Casino started as an intern in the Cyber Crimes Unit two years ago, she did not expect the stark reality she confronted in her second week on the job.
She went with the police to serve a warrant at the home of a suspected child pornographer. After the team secured the house — and made the owner put on some clothes — Casino entered to collect technological evidence: computers, phones, thumb drives and more.
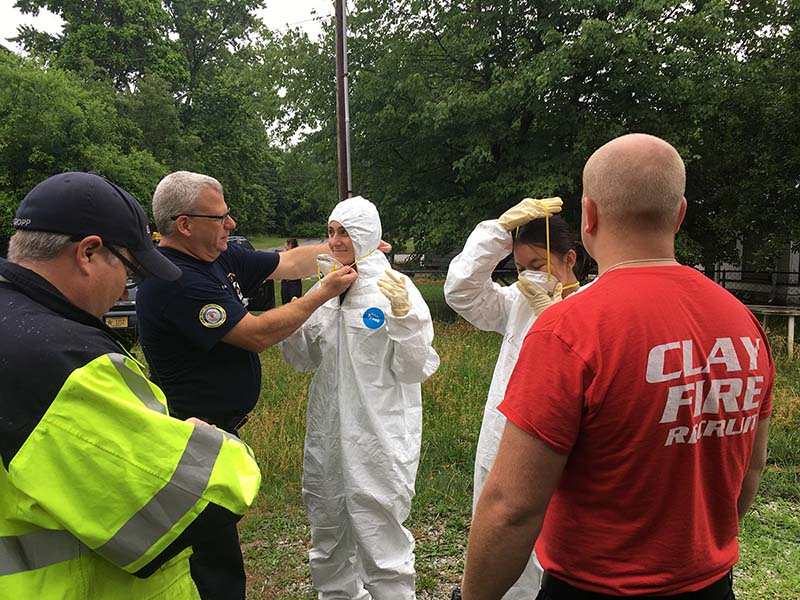
“We had to wear Hazmat suits with facemasks and Vicks under our noses,” Casino said. “It was repulsive, feces everywhere, no power, no water. The smell was so bad. I was afraid there was going to be a dead animal.”
She said the unit’s director, Mitch Kajzer, called it the second-worst house he’d seen in a long career of serving criminal warrants. For a student who grew up in Stamford, Connecticut, and went to private schools, Casino said, “It was a huge eye-opener.”
“I definitely wanted to experience that because I know I’m so sheltered,” said Casino. “I think it’s better for me that I know that exists and that I experience it now. I could get a roadblock like that and be like, ‘How do I deal with this situation?’ Now I’m way more prepared to go into any part of the U.S. or the world.”
Another seasoned senior intern, Sam Alptekin, echoed that theme.
“A lot of the education I’m getting is very technical, very mathematical,” he said. “To be able to get away from academia and find out what the real world is like, what you have to do to be successful — that is really interesting to get.”
Casino and Alptekin are two of six Notre Dame interns in the St. Joseph County Cyber Crimes Unit, which this year expanded by three spots and moved from the county jail to Hammes Mowbray Hall on campus. The students participate in every step of a cybercrime case: researching suspicious online activity, building suspect profiles from social media and public records, writing warrants to get information and search homes, collecting tech evidence on site, and performing digital forensics on anything that stores bits and bytes.
The experience thrusts their classroom learning into the real world. While Notre Dame is not the only university to partner with a local police department to provide hands-on digital forensics, it is the only program that swears in its undergraduate interns as law enforcement officers with actual police powers. As a result, the students get official badges — which stay in the office — and do all the unit’s investigative work, save the dangerous initial entry into a suspect’s home.


“What the community gets out of it is very high-quality workers who come into it with a lot of native knowledge,” said Kajzer. “They’re very adept with technology. There’s probably not a day that goes by that I don’t ask one of them something about a new technology.”
Program growth
While the county’s Cyber Crimes Unit began in 2003, the internship started when Kajzer returned to the unit in 2015. He was teaching at the time in Notre Dame’s Idzik Computing and Digital Technologies (CDT) program. He noticed that a student in his forensics class had been accepted as one of a few general interns in the county prosecutor’s office.
Kajzer asked the student if he was interested in working instead in cybercrimes. When that worked out, as did another intern the next semester, Kajzer went to Chuck Crowell, the director of the CDT minor, to formalize the relationship. With support from the consulting firm Deloitte, they were able to launch the program with three interns.
“Our thought was, if we get a sophomore, they will walk out the door with three years of experience doing some really incredible things,” Crowell said. “They’ll be irresistible to employers at that point.”
In one notable early success, the owner of a Granger tanning salon was convicted and sentenced to four years for filming nude or partially nude women during spray tans. After one victim caught him filming on her own video, a student investigator discovered two more illegal videos in a cloud account connected to the owner’s business computer, including a 17-year-old who also did not consent to being recorded.
“My hope is that we will have dozens of students that will help solve the crimes that are the hardest for law enforcement to solve.”
St. Joseph County Prosecutor Ken Cotter said moving the cybercrime office to campus provides more space and resources for the students, allowing them to balance work with their studies.
“My hope is that we will have dozens of students that will help solve the crimes that are the hardest for law enforcement to solve,” Cotter said.
This year, 22 students with a range of majors from film studies to economics applied for four open spots. With the expansion to six students this year, the unit for the first time caught up with its caseload — 181 cases in mid-November. Clearing out the backlog, Kajzer said, “is really unheard of” in any police unit in an era of tight government budgets.
Across the country, backlogs at digital forensics labs are often six to nine months, Kajzer said, and locally that process sometimes took a year. During that time, suspected predators often remain free to do more harm while the incriminating evidence sits waiting in a lab.
At Notre Dame, the student investigators regularly process cell phones in just four hours for cases ranging from child exploitation to drug sales and even murder.
“I knew we could get through more investigations with the extra manpower, which would then open up the avenues for the second prong, which is the research part of it,” Kajzer said. “Figuring out new ways to use technology to aid investigations — that’s really exciting.”

On a cold Friday morning in November, the students watched a training video on the information collected by Apple watches, Fitbits and other wearable technology. Their discussion was practical if a bit morbid: whether a heart rate monitor would record a person’s time of death or simply shut off if the person wearing one died. Hard to test that.
“What we’re looking at today is pattern-of-life information,” Kajzer said. “Not just a point in time where a crime happened, but the whole pattern of what their day was, where they went and who they were with.”
In the unit’s campus office, Kajzer wears a gun and bulletproof vest but acts as much like a professor as a police officer, discussing methods and theory from the pervasiveness of technology to the limits of privacy.
Another research project involves the discovery of a little-known cache of phone data tracking location for anyone using Google Cloud. Kajzer recently used the location data to definitively exonerate a suspect who claimed he was not present at the time and location of a crime. Alptekin is researching a new way to map that data without the help of a website that recently shut down.
“The info is in the cloud, so I can write a warrant to Google to get that file,” said Alptekin, a computer science major. “People know about it but don’t seem too concerned about privacy.”
Writing warrants
Cybercrime investigations generally involve a series of warrants, not just the well-known warrant needed to search a home. Following a recently closed case from start to finish can illustrate the elaborate legal process followed in these investigations.
Matt Ridenour, a 30 year-old Mishawaka man, was sentenced to 15 years in prison for possessing and creating child pornography on Nov. 14, making it possible to talk openly about the case. It began in March 2017, when Eric Tamashasky, a deputy prosecutor who also teaches courses in the CDT program, downloaded a contraband video through a peer-to-peer sharing program.
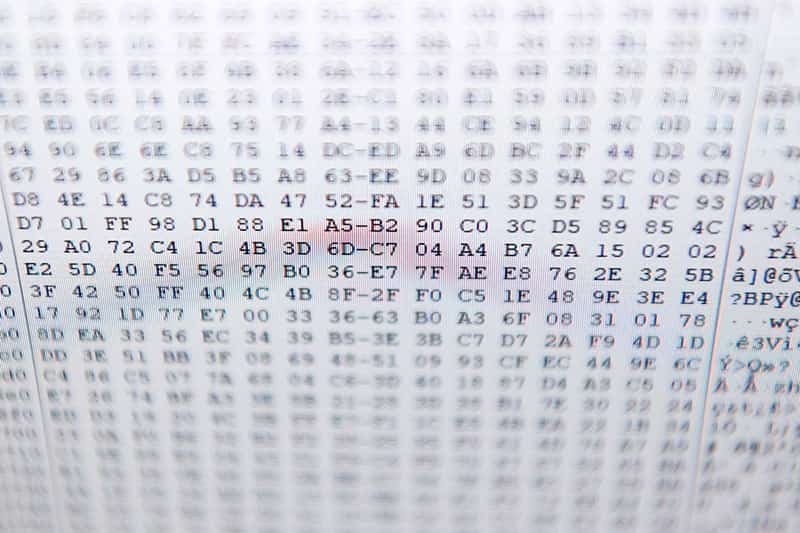
Tamashasky wrote a subpoena to Comcast to provide the account owner of the sharing computer’s IP address, which is a unique string of numbers assigned to each device connected to a computer network that uses the Internet Protocol for communication.
Many of the unit’s cases involve child exploitation, and most begin with a tip from the National Center for Missing and Exploited Children (NCMEC). When an online company such as Google or Dropbox finds that a known child porn image was downloaded using its service, the company alerts NCMEC. If the IP address geo-locates to St. Joseph County, NCMEC sends the information to the Cyber Crimes Unit at Notre Dame. Kajzer generally scans the images first to relieve the students of that burden, but only after writing a warrant to himself to allow looking at the company’s files now on his computer.
Since Tamashasky had already viewed Ridenour’s images, Kajzer assigned the case to Casino on July 5, 2017.
Armed with the name of the IP address owner, Casino used open-source intelligence techniques to build a profile of the suspect. She checked everything from social media sites and relatives to property and arrest records, taking a screen shot of any hits to copy into a detailed report that eventually ran to 37 pages. She pasted in phone numbers, birth dates, social media pictures and more.
“We know so much more about you than you even know,” Casino said. “It’s all online and public, and we take advantage of that for our investigations.”
Casino quickly identified that three people lived in the Ridenour home, and that the likely suspect was the son of the IP address owner. She could have written warrants to obtain private Facebook information or to connect his screen names to the ownership of various social media accounts, but neither was necessary in this case. Next, Kajzer drove her by the house in Mishawaka to take pictures, providing license plate numbers to check for ownership records.
Casino wrote a warrant and received a judge’s approval to search the Ridenour home on July 11, just six days after starting the case.
“It’s usually cut and dried,” Alptekin said. “It’s very definitive when we find incriminating evidence. It’s very rare to find a picture with an explanation.”
Forensic process
Casino and another intern put on their badges and bulletproof vests for the raid. They met to review the plan with other police officers and Tamashasky at a staging area, where Kajzer turned on his body cam video.
After a short drive, the students sat in the car about a block away while Kajzer and eight or nine other officers surrounded the house. The officers knocked and called and received no response, but they found that the back door was open and entered. The video shows Kajzer’s gun drawn in front while a disoriented and shirtless Ridenour walks into the kitchen. The officers scream directions and cuff him.

After the house is cleared, Casino and another intern entered with evidence kits, including rubber gloves, notepads and tech supplies. They connected to the suspect’s computer to preview evidence, which can be useful in questioning the suspect. They collected anything that stores digital information, logged it and took it back to the lab for forensic analysis.
The first step is to make a digital copy of all data that preserves the original evidence intact. The interns are trained on a forensics tool called Magnet AXIOM, which Casino used to divide the data into categories. The interns used to have to scan through hundreds or thousands of thumbnail pictures, but the program can now search, for instance, for images with more than 60 percent skin tone.
Inspecting the media section, Casino found that Ridenour had been using a screenshot program to record video chats with underage boys on an international chat site called Omegle. His laptop stored more than 300 videos of these chats involving nudity.
“That constitutes creating child pornography, so then he was taken into custody,” Casino said. “It eventually became a federal case.”
“The amount of data coming off phones these days is absurd.”
Casino traced Ridenour’s history of downloading the programs he used, plus transferring the videos to another hard drive for storage. She also wrote a warrant to Omegle to provide the IP addresses of all the computers from Ridenour’s illegal chats. She matched the times and addresses in an attempt to identify, geo-locate and inform parents about this predatory behavior.
The detailed report is crucial because cases can take years to go through the criminal court process. The students could be called to testify in court, though none have so far because most of the cases don’t go to trial.
“We do the best investigation we can and then turn it over to the second part of the criminal justice system,” Kajzer said. “We can’t control the rest, so I try not to get emotionally involved.”
Many cybercrime cases do not involve endangering children. Homicides and drug trafficking often involve phones that have been confiscated during an arrest. Some suspects provide their password, but the police can also use various password bypassing techniques if needed, plus a special bag that prevents anyone from remotely wiping the phone.

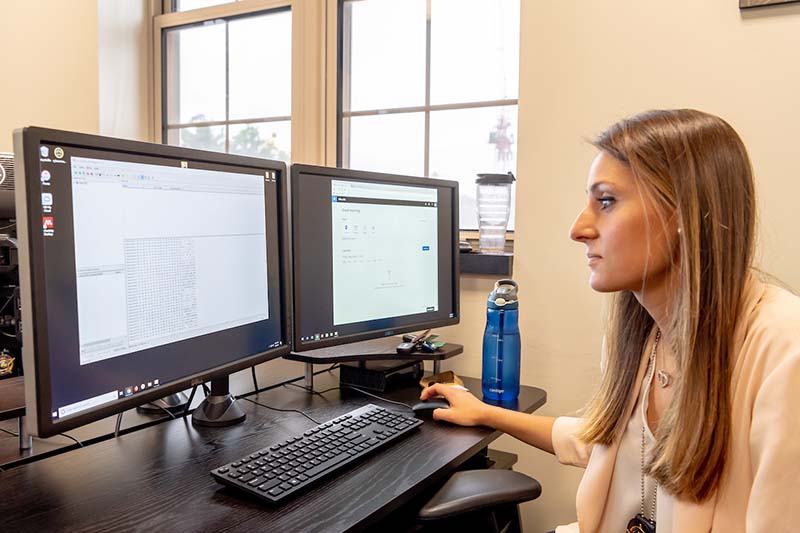
“The first phone I ever went through was a homicide phone,” Casino said. “Those are interesting. You usually have one or two phones in those situations. You can upload them together into AXIOM and filter them, so you can find if these two phones talked to each other, and you want to find these conversations only. The amount of data coming off phones these days is absurd.”
Inspiring students
Alptekin had planned to go into computer programming, but he said working in forensics has shown him a different path. Handling a serious responsibility as an undergraduate boosted his confidence about other careers.
“I was surprised by how much faith they had, the amount of work they expected us to do,” he said. “They said we’d be officers with full police power. I figured not really, but they trained us properly and expected us to operate at the level of full investigator, which was really cool and a little daunting at first.”
He did an internship with Amazon last summer, working in the Alexa division to refine speech recognition. He said the team had seen his resume and wanted to know all about his experience “as a cop.” He landed a job offer for after graduation.
Mike Chapple, a Mendoza College of Business analytics professor who acts as the students’ internship advisor, said the experience the students get in applying their skills sets them apart in opportunities ranging from the FBI to technology firms.
“Most of our students have some kind of internship,” Chapple said. “Being able to do that within the school year and within law enforcement is what’s unique and what gives them credibility. No other students can say they are sworn law enforcement officers and have worked on active investigations.”
For Casino, that early eye-opener also led to a change in career path. She did an internship over the summer with Deloitte in its cyber risk division and realized it was a way to combine her interest in economics and technology.
“I was planning to be in the business world — finance, trading jobs or things like that,” she said. “But once I had this internship, I decided tech is the way to go. It’s involved in every aspect of the world — look around, everyone’s on their phone and it’s not going to stop for a long time.”
Deloitte agreed and offered her a full-time job next year.
